The state of data protection for charities in the UK shifted in 2023, when the Information Commissioner’s Office logged 11,074 reported personal data incidents, up from 8,799 the year before, a jump of around 26%. The figure doesn’t break out charities from corporates. But it sets the backdrop for what’s coming, and the people running small charity back offices already feel it.
Three-quarters of those 2023 incidents weren’t cyberattacks. They were human errors: emails sent to the wrong group, paperwork misplaced, attachments containing the wrong list of beneficiaries. The single most common 2024 Q1 incident type was, predictably, data emailed to the incorrect recipient, 539 cases in three months, per the ICO’s quarterly trends dashboard.
That’s not a hacking problem. That’s an operations problem.
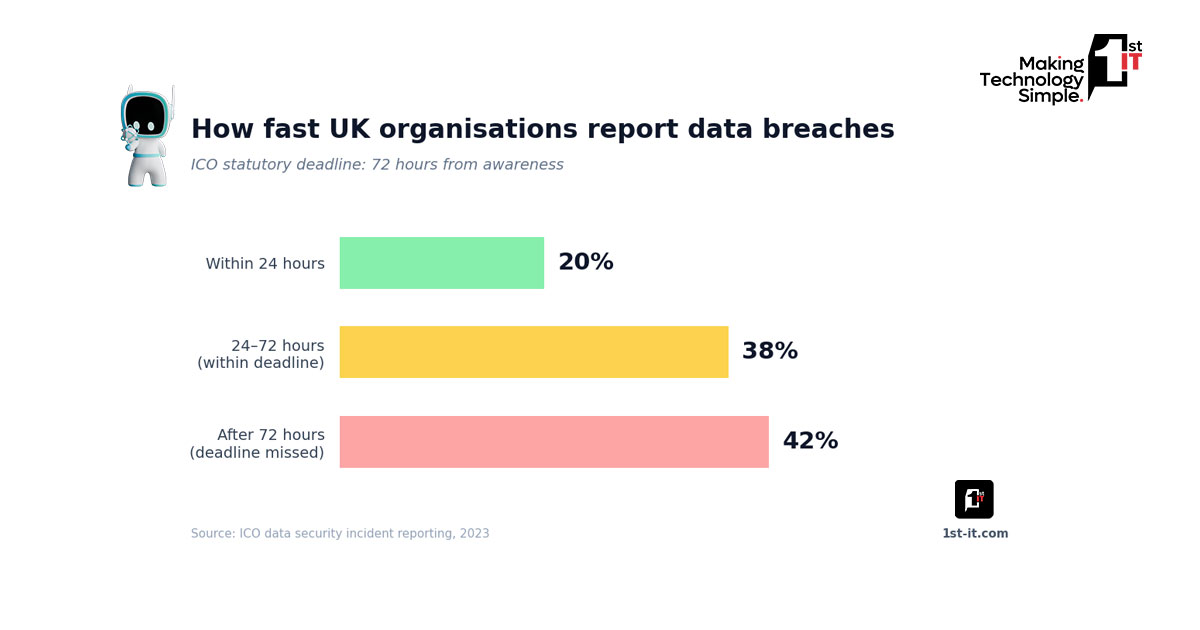
The reporting picture is worse. Around one in five UK breaches in 2023 was reported within 24 hours of discovery. Some 42% missed the 72-hour statutory deadline entirely. For a sector already stretched on time and staff, a missed deadline is the kind of thing that turns a one-line apology into a regulatory file.
The current state of data protection for charities
Until recently, the ICO treated the charity sector with a relatively soft hand. The regulator extended its 2022 “public sector approach”, fewer fines and more reprimands, to many third-sector cases. Central YMCA’s 2024 enforcement told the story well: a proposed £300,000 penalty was reduced to £7,500 after staff sent a group email about an HIV programme using “Cc” instead of “Bcc”.
That changed in 2025. Birthlink, an adoption-records charity, received an £18,000 fine after destroying thousands of irreplaceable records. The ICO explicitly stated it had departed from its softer charity stance because the breach was “highly avoidable” and caused “serious and permanent harm”. For organisations that handle health data, safeguarding records, or vulnerable beneficiary information, almost every charity really, that’s the new ceiling.
Where the gap actually sits
Charities don’t fail data protection because they don’t care. They fail it because they’re using consumer-grade tools to handle sensitive data, with rotating volunteer access, on shared laptops with no MFA. We’ve seen at least three charity IT clients, in 2024 alone, who were one phishing email away from a notifiable breach, and didn’t know their email tenant had no audit logging enabled.
The widely-shared advice isn’t wrong: write a privacy policy, train staff annually, appoint a DPO if you’re large enough. It’s just nowhere near enough. A single annual GDPR session won’t change behaviour when the same volunteer handles 200 donor records every Tuesday evening from a personal Gmail. The work is technical, not procedural, and that’s the realistic baseline for data protection for charities operating with limited budgets and rotating staff.
Most boards don’t see this until something goes wrong.
The charities that have actually moved their data protection forward did three things at once. I’m thinking of two specific clients in 2024, or maybe early 2025, both safeguarding-focused. They enforced MFA across all staff and trustees, separated personal email from charity communications, and ran proper cyber security audits twice a year rather than once. None of it is glamorous. All of it is what the ICO will look for if you’re the next reprimand.
Where this is heading
The 2025 enforcement data already tells you which way the wind is blowing. The ICO issued fewer fines than in 2024, but the average penalty climbed from £150,000 to £2.8 million. The shift is towards bigger consequences for systematic failure: missing MFA, slow incident response, no documented breach procedure. Capita’s £14 million settlement, which followed a 58-hour delay in quarantining a compromised device, was the loudest signal yet.
The Cyber Security and Resilience Bill, currently working through Parliament, will widen the ICO’s powers further, though mainly over digital service providers. Charities will feel it indirectly, through their suppliers. Your CRM vendor, your fundraising platform, your cloud backup provider: they’ll all face stricter security expectations, and the cost will pass through to your annual subscription whether you like it or not.
What the next two years won’t bring is a sudden public crackdown on small charities. The ICO doesn’t have the appetite for it, and the political optics are awful. But individual charities that handle special-category data should treat themselves as exposed regardless. That includes health, sexuality, immigration status, and beneficiary identifiers.
What good data protection for charities looks like
Three priorities cut across every charity client I’ve worked with that survived an ICO query without harm. First, MFA on everything, not just email but cloud storage, fundraising platforms, anything with personal data behind a login. Second, a written incident response plan that names two specific people, not a committee. Third, a quarterly data audit that checks who has access to what, ideally backed against a Cyber Essentials baseline rather than guesswork.
This is the quiet truth about data protection for charities in 2026: nobody’s coming to inspect you, but nobody’s going to forgive a preventable breach either. The work to fix it is small, dull, and overdue. Pick one of those three priorities and book it in this quarter.